Resources for IT, Cyber, AI and Compliance Leaders
A working library from Petronella Technology Group: deep guides, hard-won blog lessons, free assessments, on-demand training, and reference frameworks. Built by practitioners who run a Raleigh-based MSP, MSSP, and CMMC Registered Practitioner Organization since 2002.
Most resource pages are link dumps. This one is not. Every guide, blog post, and tool below has been used inside real client engagements: ransomware recoveries, CMMC Level 2 readiness assessments, HIPAA security risk assessments, AI workload buildouts, and the slow grind of getting a small business from "we have antivirus" to a defensible, audit-ready security program. If you are an IT director, CIO, compliance lead, or owner-operator trying to make sense of cybersecurity, AI adoption, and regulated industry compliance, start here.
The library is organized by what you are trying to do. If you need a strategic playbook, jump to the featured guides. If you want to learn fast on a specific topic, browse the most-read blog posts. If you need to baseline your current risk, run a free assessment. If you want structured, on-demand learning for your team, see the Training Academy. Use what you need. Skip what you do not. Everything links to deeper coverage when you want it.
A short note on point of view. Petronella Technology Group is a Raleigh-based MSP, MSSP, digital forensics shop, and CMMC Registered Practitioner Organization that has been operating in the Triangle since 2002. Our team holds CMMC-RP credentials across the bench, plus hands-on certifications in network engineering (CCNA), wireless (CWNE), and digital forensics (DFE #604180 for the founder). That background shapes every resource on this page. We do not write speculative thinkpieces about technology we have never deployed. We write about ransomware because we have done the recovery. We write about CMMC because we sit in the gap-assessment chair. We write about private AI because we run the inference servers. The library is opinionated on purpose, because most of the content out there is sponsored and most of the advice out there is generic.
One more thing. Nothing on this page sits behind a wall. There is no email gate on the blog, no credit card on the free tools, and no obligation to talk to a salesperson before you can read a guide. We share these resources because the security baseline of the small-business community is too low, and because we would rather have an educated conversation when a client does call us than spend the first thirty minutes of every prospect call explaining what zero trust actually means. If anything below sparks a question, the easiest path is to call (919) 348-4912 or schedule through the contact page. For a deeper look at downloadable research reports and executive briefs, or our engagement pricing and packages, follow those links.
Featured Guides and Playbooks
Two libraries in one. Long-form practitioner guides for working through a specific risk or program, and downloadable briefs you can hand to a board, CFO, or vendor-evaluation committee. Each one is built from delivering the same engagement repeatedly for clients across the Raleigh-Durham region and nationwide.
New · May 2026Business AI Series – Owner and IT Director Playbooks
Three printable cheatsheets every small-business owner, IT manager, and IT director should hand to their team before approving the first AI workload. Built from real client engagements, reviewed by Craig Petronella (CMMC-RP, RPO #1449), aligned to NIST AI RMF and CMMC governance expectations. Free downloads, no login required.
 Business AI Series | 01 Acceptable Use Policy
Business AI Series | 01 Acceptable Use Policy
AI Acceptable Use Policy Template | Free PDF for Small Business
A downloadable AI acceptable use policy template for owners writing their first AI governance document. Covers approved tools, sensitive-data prohibitions, prompt-injection awareness, AI-output verification, and the disciplinary framework auditors expect. Maps to CMMC AT.L2-3.2.1 and NIST AI RMF GOVERN function. Reviewed by Craig Petronella, CMMC-RP RPO #1449.
Download the AI AUP template → Business AI Series | 02 AI Readiness
Business AI Series | 02 AI Readiness
AI Readiness Checklist for Small and Mid-Market Businesses
A practitioner-grade AI readiness checklist for owners and IT directors deciding whether to deploy AI inside the business. Covers data governance, identity and access controls, vendor due diligence, model selection, human-in-the-loop design, and the compliance gates that turn an AI chatbot pilot into a defensible production rollout. Reviewed by Craig Petronella, CMMC-RP RPO #1449.
Download the AI readiness checklist → Business AI Series | 03 Ransomware Readiness
Business AI Series | 03 Ransomware Readiness
Ransomware Readiness Checklist | Owner-Operator SMB Defense
A ransomware readiness checklist for owners who would rather not learn ransomware recovery in real time. Covers immutable backups, EDR coverage gaps, lateral-movement detection, ransom-payment ethics, cyber-insurance documentation, and the tabletop drill our team runs with clients before they ever experience the worst week of their career. Reviewed by Craig Petronella, CMMC-RP RPO #1449.
Download the ransomware readiness checklist →Practitioner Guides
 For Cyberstalking and Stalkerware Victims
For Cyberstalking and Stalkerware Victims
Cyberstalking Victim Guide
A 5,368-word practitioner guide for victims of cyberstalking, stalkerware, and intimate-partner digital abuse. The first 72 hours in seven steps: evidence preservation, device hardening, attorney coordination, and realistic cost ranges. Written by a Licensed Digital Forensic Examiner (NC DFE #604180) with 22 FAQs and North Carolina plus national victim-services resources.
Read the victim guide → For Healthcare and Covered Entities
For Healthcare and Covered Entities
HIPAA Hosting Buyers Guide
Twelve vendor-evaluation questions every healthcare organization should ask before signing a Business Associate Agreement with a hosting provider. Covers BAA scope, breach-notification timelines, encryption posture, audit-log retention, and the technical safeguards OCR auditors actually look for.
Read the buyers guide → For MSPs and IT Service Firms
For MSPs and IT Service Firms
MSP Accelerator Playbook
The full operating playbook our team uses to run a profitable MSP and MSSP practice: stack design, pricing tiers, sales cadences, documentation standards, and the operator council we use for peer benchmarking. Written for owners and leadership teams that want to grow margins without burning out.
Read the playbook → For Robotics and Defense R and D Teams
For Robotics and Defense R and D Teams
Secure Robotics Development Brief
Sovereign AI for regulated robotics R and D: how to keep model training, inference, and telemetry inside your CMMC L1, L2, or L3, HIPAA, or ITAR and EAR boundary. Maps to NIST 800-171 with a working reference stack using Reachy Mini and NVIDIA Elite Partner Channel hardware.
Read the brief → Vibe Coder Series | 01 Vocabulary
Vibe Coder Series | 01 Vocabulary
AI Vocabulary | Vibe Coder Field Guide
Plain-English definitions of 22 AI and security terms every new-to-AI builder needs when shipping with Claude Code, Cursor, Copilot, or Windsurf. Each term gets a definition, a real-world example, and a one-line security note. Printable PDF lead magnet, reviewed by Craig Petronella, CMMC-RP RPO #1449.
Read the field guide →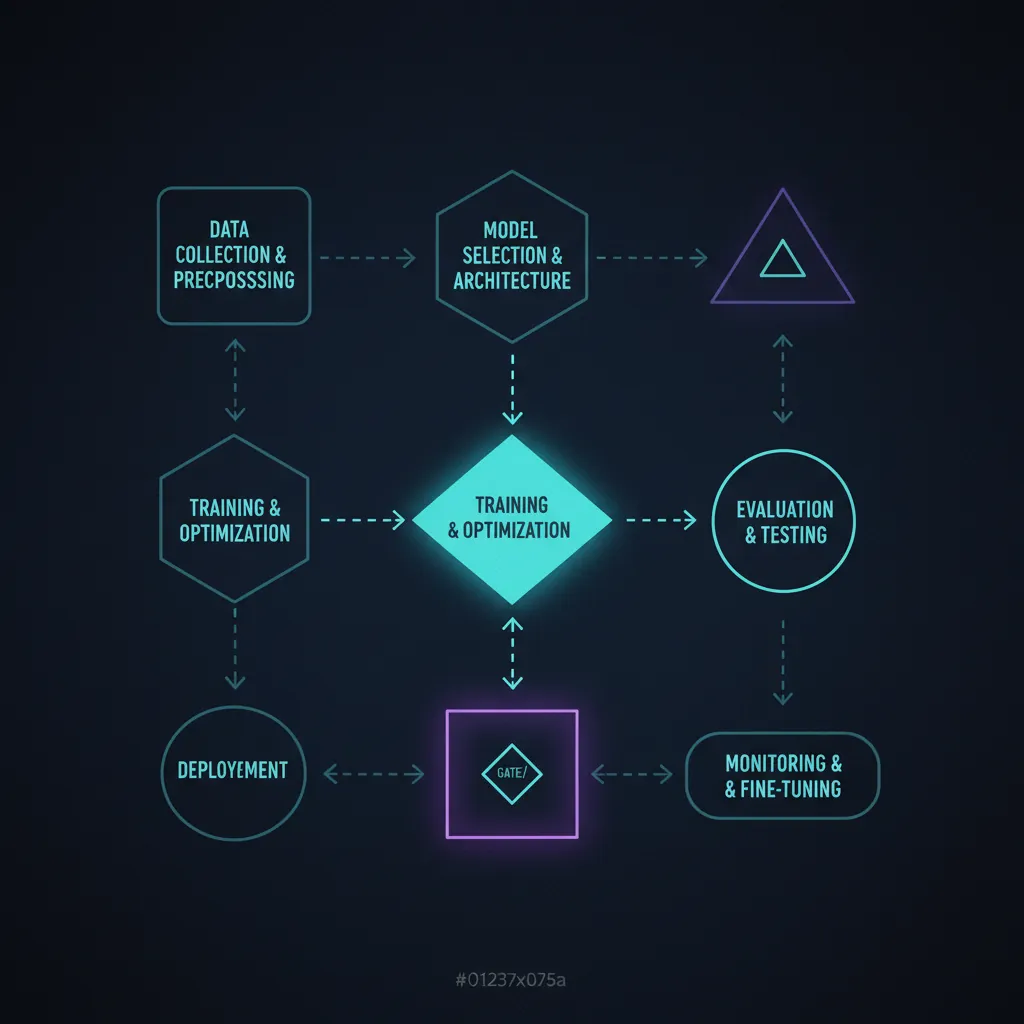 Vibe Coder Series | 02 Workflow
Vibe Coder Series | 02 Workflow
AI Coding Workflow | Vibe Coder Field Guide
The 22 repeatable moves that turn an AI session into shippable code: plan, prompt, diff-review, test loop, commit point, rollback, review gate, sandbox, audit trail, plus the agent-runaway and context-overrun risks unique to AI workflow. Reviewed by Craig Petronella, CMMC-RP RPO #1449.
Read the field guide → Vibe Coder Series | 03 Git and GitHub
Vibe Coder Series | 03 Git and GitHub
Git and GitHub | Vibe Coder Field Guide
The 22 Git and GitHub terms a non-engineer needs before the AI starts committing to real code. Repository, commit, branch, pull request, merge conflict, leaked secret in history, force push to main, plus a pre-merge ship-it gate written for the moment an AI agent is the one pushing. Reviewed by Craig Petronella, CMMC-RP RPO #1449.
Read the field guide →Downloadable Guides and Briefs
 For CTOs and IT Leaders
For CTOs and IT Leaders
AI Implementation Guide
How regulated mid-market companies actually deploy AI without sending sensitive data to public chatbots. Covers private LLM hosting, guardrails for HIPAA and CFR-controlled data, AI governance frameworks, model selection, and the practical question every CTO asks: build, buy, or fine-tune.
Read the AI guide → For Defense Contractors
For Defense Contractors
CMMC Compliance Guide
A field guide to CMMC 2.0 readiness from a Registered Practitioner Organization. Walks through Level 1, Level 2, and Level 3 expectations, the 110 NIST 800-171 controls, scoping CUI environments, building a System Security Plan, and surviving your C3PAO assessment.
Read the CMMC guide → For Healthcare and Covered Entities
For Healthcare and Covered Entities
HIPAA Compliance Guide
Plain-language coverage of the HIPAA Security Rule, Privacy Rule, and Breach Notification Rule for covered entities and business associates. Includes the security risk assessment workflow, encryption standards, workforce training cadence, and the 2026 Security Rule update timeline.
Read the HIPAA guide → For Incident Response and Triage
For Incident Response and Triage
Forensics Incident Response Playbook
A free playbook from a Licensed Digital Forensic Examiner covering the highest-frequency incident types our shop sees: SIM swap, cryptocurrency theft, ransomware, business email compromise, and wire fraud. Each scenario gets a triage workflow, evidence-preservation checklist, and escalation criteria.
Read the playbook → For Owners and Operators
For Owners and Operators
2026 SMB Cybersecurity Survival Guide
Forty-two pages of practical small-business cybersecurity strategy for 2026: compliance posture, threat prevention, budget planning, and the controls that actually move the needle when every dollar matters. Free download, no credit card, no obligation.
Read the survival guide →
Most-Read Blog Posts and Field Notes
A curated cut of the Petronella Technology Group blog. These are the posts our clients reference most often during quarterly strategy reviews, vendor evaluations, and incident postmortems. Grouped by what you are trying to figure out.
 CMMC
CMMCCMMC Level 2 Checklist: 14 Controls Most Primes Fail
The fourteen NIST 800-171 controls that consistently trip up first-time assessees, with the exact policy and evidence patterns that pass.
Read post →
CMMCWhat Is CMMC: Complete Guide for Defense Contractors 2026
The whole certification ecosystem, plain-spoken: levels, timelines, Joint Surveillance, C3PAO selection, and what changes in 2026.
Read post →
CMMCBest CMMC Compliance Software 2026: 3 Top Tools Compared
Honest, hands-on comparison of the leading CMMC documentation platforms based on real assessment delivery, not vendor briefings.
Read post →
CMMCCMMC Level 2 for Small Defense Contractors: Practical Guide
Right-sized roadmap for sub-fifty-employee primes and subs that still need a defensible CUI enclave and SSP.
Read post →
 HIPAA
HIPAAHIPAA Security Rule 2026 Update: Q3 Deadlines for CEs
What the proposed Security Rule update changes, the new technical safeguards, and the realistic remediation runway for covered entities.
Read post →
HIPAAHIPAA Security Risk Assessment: Step by Step
The exact workflow our analysts use to deliver an OCR-defensible SRA, including evidence-collection templates and scoring rubrics.
Read post →
HIPAAHIPAA Compliance Checklist 2026: Step by Step
Comprehensive checklist mapping every Security Rule safeguard to the implementation specs, addressable items, and evidence artifacts auditors expect.
Read post →
HIPAAHealthcare Compliance Training: HIPAA and Beyond
Building an annual workforce training program that satisfies HIPAA, state privacy law, and the security awareness expectations of cyber insurers.
Read post →
 Private AI
Private AIPrivate AI for CTOs: Why Regulated Teams Leave ChatGPT
Why mid-market CTOs in healthcare, defense, and finance are pulling AI workloads in-house, and what the production architecture looks like.
Read post →
Private AIPrivate AI vs Cloud AI: Enterprise On-Premise Comparison
Side-by-side cost, latency, data-sovereignty, and compliance comparison for teams choosing between cloud APIs and on-prem inference.
Read post →
AI SecurityAI Threat Detection 2026: How AI Transforms Cybersecurity
Where AI genuinely improves SOC outcomes, where it generates false confidence, and the human controls that keep automated response sane.
Read post →
AI GovernanceAI Governance for Business: A Practical Framework Guide
A workable governance model: roles, review gates, model registries, and the policy artifacts auditors and the board both want.
Read post →
AI InfrastructureAI Workstation vs Cloud GPU: 2026 Cost Guide
Real numbers from real builds: when an in-office workstation pays back faster than rented GPU minutes, and when it does not.
Read post →
Private AIPrivate LLM Deployment: Run AI Without the Cloud in 2026
Reference architecture for self-hosted Llama, Mistral, and Qwen workloads behind your firewall, including hardware sizing.
Read post →
AI for RetailAI for Retail: Demand Forecasting and Inventory Optimization
How retailers use private AI for demand forecasting, inventory optimization, and loss prevention without shipping sales data to a public model.
Read post →
AI SecurityApril Fools Cyber Drill for GenAI Apps Without the Pranks
A tabletop red-team exercise for generative AI applications - run a controlled drill against prompt injection and data leakage without disrupting production.
Read post →
AI SecurityCX That Outsmarts Deepfakes and Voice Clones
How customer-experience teams verify identity and harden voice channels against deepfake audio and AI voice cloning without adding friction for real callers.
Read post →
AI GovernanceHard-Won Lessons from Rolling Out Microsoft Copilot at Scale
What enterprise Copilot deployments teach about data-access scoping, oversharing risk, and the governance controls regulated teams need before going wide.
Read post →
AI SecurityDon't Get Pranked: Red Team Your AI Before They Do
A practical guide to red-teaming your AI systems - the prompt-injection, jailbreak, and data-exfiltration tests to run before an attacker finds the gaps first.
Read post →
AI SecurityOutsmart Deepfakes in Your Contact Center
Deepfake voice attacks are targeting contact centers. The caller-verification, liveness, and agent-training controls that stop AI voice clones from social-engineering your staff.
Read post →
 Incident Response
Incident ResponseIncident Response Retainer: Why Every Business Needs One Before a Breach
What a retainer actually buys you, the response-time math, and how to evaluate IR firms before you have an emergency on your hands.
Read post →
Incident ResponseIncident Response Plan Template: Free Download Guide
Six-phase IR plan template aligned with NIST SP 800-61, with role assignments, communications scripts, and notification triggers ready to fill in.
Read post →
AwarenessPhishing Simulation Training: Build a Human Firewall
How to design a phishing simulation program that lowers click rates without burning out staff or generating compliance theater.
Read post →
AwarenessRansomware Training for Employees: Prevention Program
What the training curriculum should cover, who should attend, how often to refresh, and the metrics that prove it actually changed behavior.
Read post →
Zero TrustZero Trust Security Model: A Complete Business Guide
Zero trust without the buzzwords: identity, device posture, network segmentation, and the realistic 12 to 18-month rollout for mid-market.
Read post →
Zero TrustTop 10 Zero Trust Vendors for SMBs 2026: Price and Features
Side-by-side scorecard of the ten zero-trust platforms that actually price and deploy for sub-thousand-seat organizations.
Read post →
Zero TrustZero Trust vs VPN: Modern Remote Access in 2026
Why zero trust network access is replacing the legacy VPN, the security gaps a flat VPN tunnel leaves open, and a realistic migration path for mid-market teams.
Read post →
AuditCyber Security Audit Checklist (2026): 60+ Items
The internal-audit checklist our vCISO team uses for quarterly client reviews, structured around CIS Controls v8 and NIST CSF 2.0.
Read post →
 AI Agents
AI AgentsOpenClaw: Open-Source AI Agent Framework Guide
Practical setup, configuration, and security review of the open-source agent framework our team uses for internal automation.
Read post →
AI DevAI-Powered Development with Claude Code: Workflow Guide
How an MSP and security team uses an AI coding assistant safely, including prompt scoping, secret hygiene, and review gates.
Read post →
AI AutomationAI Automation for Small Business: Save 20+ Hours a Week
Concrete automation patterns for back-office work that survive audit, with examples from finance, scheduling, and customer support.
Read post →
Custom AICustom AI Chatbot Development for Business
What goes into a defensible custom chatbot: data sourcing, retrieval design, guardrails, evaluation, and the part most vendors skip.
Read post →
 Claude
ClaudeClaude Design Principles for Regulated AI Builds
How Anthropic's Claude design and safety-first philosophy translates into production AI tooling for regulated industries. Lessons from Raleigh NC.
Read post →
ClaudeThe Claude Mythos: Why Anthropic Is Winning Enterprise AI
Why Claude overtook OpenAI in enterprise AI share, what Constitutional AI means for regulated industries, and how Petronella built its agent fleet on it.
Read post →
Claude SDKClaude SDK: Ship Production AI Agents Safely
Build production AI agents on the Claude SDK. Petronella Technology Group shows the architecture, tool use, prompt caching, rate limits, and test harness.
Read post →
ClaudePaperclip for Claude: How to Vet AI Extensions Safely
Paperclip for Claude turns Claude Code agents into a coordinated team. What it does, where the risks sit, and how to vet plugins before touching client data.
Read post →
AI ToolingCmux: The AI Agent Terminal for Regulated Dev Shops
What Cmux is, how it compares to tmux and Zellij, and the compliance questions Raleigh dev teams must answer before giving AI assistants shell access.
Read post →
AI CodingOpenCode, Antigravity, and Gemma 4: Safe AI Coding Tools
Comparing OpenCode, Google Antigravity, and Gemma 4 for CMMC and HIPAA-regulated teams. Which AI coding tools keep code local, and which ship it to the cloud?
Read post →
AI CodingPi.dev Review: Terminal Coding Agent for Regulated Teams
Pi.dev is a minimal open-source terminal coding agent. Review covers what it does, the install, the risks for regulated businesses, and how to adopt safely.
Read post →
Open Source AIHermes Agent: Open-Source AI for Regulated Businesses
Hermes Agent from Nous Research runs self-hosted AI on your own infrastructure. See when it beats Claude and GPT for CMMC, HIPAA, and data sovereignty.
Read post →
Local AIJan AI Review: Local-First LLMs for Regulated Businesses
Honest review of Jan AI, the open-source local-first ChatGPT alternative. When it fits regulated businesses and when you outgrow it for a private AI cluster.
Read post →
AI ResearchKarpathy's Autoresearch: What It Means for Enterprise R&D
Andrej Karpathy's autoresearch loop runs AI experiments overnight on a single GPU. Here is what it means for regulated businesses and how to experiment safely.
Read post →
AI VideoSeedance 2.0 for Business Video: What Owners Need to Know
Seedance 2.0 is ByteDance's new AI video model. How it compares to Sora 2, Veo 3, Runway, Kling, and Pika, with a compliance and brand-safety lens for owners.
Read post →
AI HardwareAI Workstation 2026: RTX 5090 Deep Learning Build
Full build guide for a 2026 AI workstation built around the RTX 5090, covering chassis, thermals, CUDA toolchain, and the deep-learning workloads it handles.
Read post →
InfrastructureMigrate VMware ESXi to Proxmox VE: Step by Step
Complete migration runbook for moving production workloads off VMware ESXi to Proxmox VE, with pre-flight checks, network mapping, and rollback paths.
Read post →
BackupProxmox Backup Server: Production Configuration Guide
Configure Proxmox Backup Server for real-world recovery: datastores, verification, garbage collection, encryption, and restore drills that actually work.
Read post →
InfrastructureProxmox vs Docker: When to Use Each in 2026
Virtualization or containers. Both earn their keep. This guide explains when Proxmox belongs in the stack, when Docker wins, and how they compose cleanly.
Read post →
HostingWordPress Migration Guide: Keep SEO, Move Off Slow Hosts
Step-by-step WordPress migration guide from Wix, Squarespace, Joomla, Drupal, or slow shared hosting. Preserve SEO, minimize downtime, and keep every ranking.
Read post →
HostingFrom GoDaddy to Custom Managed Hosting: Business Case
GoDaddy shared hosting throttles CPU, pushes upsells, and carries a documented FTC security record. Petronella offers faster, safer custom managed hosting.
Read post →
 CMMC
CMMCCMMC Enclave: Strategy, Tradeoffs, and 2026 Options
A 2026 guide to CMMC enclaves: segmentation, build versus buy, monthly cost ranges, failure modes, and evidence collection.
Read post →
CMMCCMMC Level 2 Checklist: 14 Domain Readiness Guide
A practical CMMC Level 2 checklist walking through all 14 NIST 800-171 domains, common gaps, and when to bring in a C3PAO.
Read post →
CompliancePrivate Cloud for CMMC and HIPAA: Commodity Cloud Trap
AWS GovCloud and GCC High are not automatic compliance. See where commodity cloud breaks CMMC, HIPAA, FINRA, and attorney ethics, and when a private cloud wins.
Read post →
Data SovereigntyPrivate Cloud vs iCloud and Google Drive: Who Owns Data?
iCloud, Google Drive, and OneDrive are convenient, but your data lives on their terms. Why regulated and privacy-aware owners should evaluate a private cloud.
Read post →
Data ProtectionData Loss Prevention Strategy for 2026
Most sensitive data leaves through honest mistakes, not malice. Build a DLP program that covers email, endpoints, SaaS, and the audit evidence auditors expect.
Read post →
Network SecurityNetwork Segmentation Best Practices Guide
After initial access the attacker moves laterally. This segmentation guide covers VLAN design, microsegmentation, east-west controls, and the evidence auditors want.
Read post →
Pen TestingPenetration Testing Methodology Explained
Every organization has security gaps. Learn the reconnaissance, exploitation, post-exploit, and reporting stages ethical hackers follow, and what to buy.
Read post →
Zero TrustZero Trust Rules for GenAI Email Triage and HIPAA-Safe
Healthcare teams use GenAI to triage patient email. Here are the Zero Trust rules that keep the workflow HIPAA-safe and auditable.
Read post →
Zero TrustZero Trust with Passkeys for Customer Identity
Passkey-based customer identity in contact centers: how to combine Zero Trust, passkeys, and agent tooling for safer identity verification at scale.
Read post →
Zero TrustZero Trust for Agentic CRM Data Sharing Without Shadow Work
Grant AI agents minimum-scope CRM access, prove every action was sanctioned, and avoid the shadow work that auditors flag.
Read post →
CMMC ToolFree CMMC Self-Score Worksheet
Score your current CMMC readiness across the 110 NIST 800-171 controls in one downloadable worksheet. See where gaps live before a C3PAO visit.
Read post →
Local SEOAI SEO for Small Business: Get Found in 2026
How small businesses can use AI for SEO in 2026. Covers AI content tools, Google AI Overviews, local SEO automation, and getting cited by ChatGPT and Perplexity.
Read post →
Local SEOGoogle Maps SEO: Rank Your Business in 2026
Complete Google Business Profile optimization guide. Rank higher in Google Maps with NAP consistency, reviews, photos, posts, and local SEO strategies.
Read post →
 SMB Security
SMB Security10 Cybersecurity Tips for Small Businesses
The ten highest-leverage security moves a small business can make this quarter. Written for owners who have to make every dollar count.
Read guide →
Endpoint3 Ways Old Antivirus Leaves Your Business Vulnerable
Traditional antivirus missed modern ransomware, fileless malware, and living-off-the-land attacks. Here is what to replace it with, and why.
Read guide →
RansomwareWannaCry Ransomware: Field Notes and Lessons
The WannaCry outbreak reshaped how Petronella Technology Group runs ransomware defense. These field notes explain what still protects businesses today.
Read guide →
CMMC Level 2 Checklist: 14 Controls Most Primes Fail
The fourteen NIST 800-171 controls that consistently trip up first-time assessees, with the exact policy and evidence patterns that pass.
Read post → CMMCWhat Is CMMC: Complete Guide for Defense Contractors 2026
The whole certification ecosystem, plain-spoken: levels, timelines, Joint Surveillance, C3PAO selection, and what changes in 2026.
Read post → CMMCBest CMMC Compliance Software 2026: 3 Top Tools Compared
Honest, hands-on comparison of the leading CMMC documentation platforms based on real assessment delivery, not vendor briefings.
Read post → CMMCCMMC Level 2 for Small Defense Contractors: Practical Guide
Right-sized roadmap for sub-fifty-employee primes and subs that still need a defensible CUI enclave and SSP.
Read post →
HIPAA Security Rule 2026 Update: Q3 Deadlines for CEs
What the proposed Security Rule update changes, the new technical safeguards, and the realistic remediation runway for covered entities.
Read post → HIPAAHIPAA Security Risk Assessment: Step by Step
The exact workflow our analysts use to deliver an OCR-defensible SRA, including evidence-collection templates and scoring rubrics.
Read post → HIPAAHIPAA Compliance Checklist 2026: Step by Step
Comprehensive checklist mapping every Security Rule safeguard to the implementation specs, addressable items, and evidence artifacts auditors expect.
Read post → HIPAAHealthcare Compliance Training: HIPAA and Beyond
Building an annual workforce training program that satisfies HIPAA, state privacy law, and the security awareness expectations of cyber insurers.
Read post →
 Private AI
Private AIPrivate AI for CTOs: Why Regulated Teams Leave ChatGPT
Why mid-market CTOs in healthcare, defense, and finance are pulling AI workloads in-house, and what the production architecture looks like.
Read post →
Private AIPrivate AI vs Cloud AI: Enterprise On-Premise Comparison
Side-by-side cost, latency, data-sovereignty, and compliance comparison for teams choosing between cloud APIs and on-prem inference.
Read post →
AI SecurityAI Threat Detection 2026: How AI Transforms Cybersecurity
Where AI genuinely improves SOC outcomes, where it generates false confidence, and the human controls that keep automated response sane.
Read post →
AI GovernanceAI Governance for Business: A Practical Framework Guide
A workable governance model: roles, review gates, model registries, and the policy artifacts auditors and the board both want.
Read post →
AI InfrastructureAI Workstation vs Cloud GPU: 2026 Cost Guide
Real numbers from real builds: when an in-office workstation pays back faster than rented GPU minutes, and when it does not.
Read post →
Private AIPrivate LLM Deployment: Run AI Without the Cloud in 2026
Reference architecture for self-hosted Llama, Mistral, and Qwen workloads behind your firewall, including hardware sizing.
Read post →
AI for RetailAI for Retail: Demand Forecasting and Inventory Optimization
How retailers use private AI for demand forecasting, inventory optimization, and loss prevention without shipping sales data to a public model.
Read post →
AI SecurityApril Fools Cyber Drill for GenAI Apps Without the Pranks
A tabletop red-team exercise for generative AI applications - run a controlled drill against prompt injection and data leakage without disrupting production.
Read post →
AI SecurityCX That Outsmarts Deepfakes and Voice Clones
How customer-experience teams verify identity and harden voice channels against deepfake audio and AI voice cloning without adding friction for real callers.
Read post →
AI GovernanceHard-Won Lessons from Rolling Out Microsoft Copilot at Scale
What enterprise Copilot deployments teach about data-access scoping, oversharing risk, and the governance controls regulated teams need before going wide.
Read post →
AI SecurityDon't Get Pranked: Red Team Your AI Before They Do
A practical guide to red-teaming your AI systems - the prompt-injection, jailbreak, and data-exfiltration tests to run before an attacker finds the gaps first.
Read post →
AI SecurityOutsmart Deepfakes in Your Contact Center
Deepfake voice attacks are targeting contact centers. The caller-verification, liveness, and agent-training controls that stop AI voice clones from social-engineering your staff.
Read post →
 Incident Response
Incident ResponseIncident Response Retainer: Why Every Business Needs One Before a Breach
What a retainer actually buys you, the response-time math, and how to evaluate IR firms before you have an emergency on your hands.
Read post →
Incident ResponseIncident Response Plan Template: Free Download Guide
Six-phase IR plan template aligned with NIST SP 800-61, with role assignments, communications scripts, and notification triggers ready to fill in.
Read post →
AwarenessPhishing Simulation Training: Build a Human Firewall
How to design a phishing simulation program that lowers click rates without burning out staff or generating compliance theater.
Read post →
AwarenessRansomware Training for Employees: Prevention Program
What the training curriculum should cover, who should attend, how often to refresh, and the metrics that prove it actually changed behavior.
Read post →
Zero TrustZero Trust Security Model: A Complete Business Guide
Zero trust without the buzzwords: identity, device posture, network segmentation, and the realistic 12 to 18-month rollout for mid-market.
Read post →
Zero TrustTop 10 Zero Trust Vendors for SMBs 2026: Price and Features
Side-by-side scorecard of the ten zero-trust platforms that actually price and deploy for sub-thousand-seat organizations.
Read post →
Zero TrustZero Trust vs VPN: Modern Remote Access in 2026
Why zero trust network access is replacing the legacy VPN, the security gaps a flat VPN tunnel leaves open, and a realistic migration path for mid-market teams.
Read post →
AuditCyber Security Audit Checklist (2026): 60+ Items
The internal-audit checklist our vCISO team uses for quarterly client reviews, structured around CIS Controls v8 and NIST CSF 2.0.
Read post →
 AI Agents
AI AgentsOpenClaw: Open-Source AI Agent Framework Guide
Practical setup, configuration, and security review of the open-source agent framework our team uses for internal automation.
Read post →
AI DevAI-Powered Development with Claude Code: Workflow Guide
How an MSP and security team uses an AI coding assistant safely, including prompt scoping, secret hygiene, and review gates.
Read post →
AI AutomationAI Automation for Small Business: Save 20+ Hours a Week
Concrete automation patterns for back-office work that survive audit, with examples from finance, scheduling, and customer support.
Read post →
Custom AICustom AI Chatbot Development for Business
What goes into a defensible custom chatbot: data sourcing, retrieval design, guardrails, evaluation, and the part most vendors skip.
Read post →
 Claude
ClaudeClaude Design Principles for Regulated AI Builds
How Anthropic's Claude design and safety-first philosophy translates into production AI tooling for regulated industries. Lessons from Raleigh NC.
Read post →
ClaudeThe Claude Mythos: Why Anthropic Is Winning Enterprise AI
Why Claude overtook OpenAI in enterprise AI share, what Constitutional AI means for regulated industries, and how Petronella built its agent fleet on it.
Read post →
Claude SDKClaude SDK: Ship Production AI Agents Safely
Build production AI agents on the Claude SDK. Petronella Technology Group shows the architecture, tool use, prompt caching, rate limits, and test harness.
Read post →
ClaudePaperclip for Claude: How to Vet AI Extensions Safely
Paperclip for Claude turns Claude Code agents into a coordinated team. What it does, where the risks sit, and how to vet plugins before touching client data.
Read post →
AI ToolingCmux: The AI Agent Terminal for Regulated Dev Shops
What Cmux is, how it compares to tmux and Zellij, and the compliance questions Raleigh dev teams must answer before giving AI assistants shell access.
Read post →
AI CodingOpenCode, Antigravity, and Gemma 4: Safe AI Coding Tools
Comparing OpenCode, Google Antigravity, and Gemma 4 for CMMC and HIPAA-regulated teams. Which AI coding tools keep code local, and which ship it to the cloud?
Read post →
AI CodingPi.dev Review: Terminal Coding Agent for Regulated Teams
Pi.dev is a minimal open-source terminal coding agent. Review covers what it does, the install, the risks for regulated businesses, and how to adopt safely.
Read post →
Open Source AIHermes Agent: Open-Source AI for Regulated Businesses
Hermes Agent from Nous Research runs self-hosted AI on your own infrastructure. See when it beats Claude and GPT for CMMC, HIPAA, and data sovereignty.
Read post →
Local AIJan AI Review: Local-First LLMs for Regulated Businesses
Honest review of Jan AI, the open-source local-first ChatGPT alternative. When it fits regulated businesses and when you outgrow it for a private AI cluster.
Read post →
AI ResearchKarpathy's Autoresearch: What It Means for Enterprise R&D
Andrej Karpathy's autoresearch loop runs AI experiments overnight on a single GPU. Here is what it means for regulated businesses and how to experiment safely.
Read post →
AI VideoSeedance 2.0 for Business Video: What Owners Need to Know
Seedance 2.0 is ByteDance's new AI video model. How it compares to Sora 2, Veo 3, Runway, Kling, and Pika, with a compliance and brand-safety lens for owners.
Read post →
AI HardwareAI Workstation 2026: RTX 5090 Deep Learning Build
Full build guide for a 2026 AI workstation built around the RTX 5090, covering chassis, thermals, CUDA toolchain, and the deep-learning workloads it handles.
Read post →
InfrastructureMigrate VMware ESXi to Proxmox VE: Step by Step
Complete migration runbook for moving production workloads off VMware ESXi to Proxmox VE, with pre-flight checks, network mapping, and rollback paths.
Read post →
BackupProxmox Backup Server: Production Configuration Guide
Configure Proxmox Backup Server for real-world recovery: datastores, verification, garbage collection, encryption, and restore drills that actually work.
Read post →
InfrastructureProxmox vs Docker: When to Use Each in 2026
Virtualization or containers. Both earn their keep. This guide explains when Proxmox belongs in the stack, when Docker wins, and how they compose cleanly.
Read post →
HostingWordPress Migration Guide: Keep SEO, Move Off Slow Hosts
Step-by-step WordPress migration guide from Wix, Squarespace, Joomla, Drupal, or slow shared hosting. Preserve SEO, minimize downtime, and keep every ranking.
Read post →
HostingFrom GoDaddy to Custom Managed Hosting: Business Case
GoDaddy shared hosting throttles CPU, pushes upsells, and carries a documented FTC security record. Petronella offers faster, safer custom managed hosting.
Read post →
 CMMC
CMMCCMMC Enclave: Strategy, Tradeoffs, and 2026 Options
A 2026 guide to CMMC enclaves: segmentation, build versus buy, monthly cost ranges, failure modes, and evidence collection.
Read post →
CMMCCMMC Level 2 Checklist: 14 Domain Readiness Guide
A practical CMMC Level 2 checklist walking through all 14 NIST 800-171 domains, common gaps, and when to bring in a C3PAO.
Read post →
CompliancePrivate Cloud for CMMC and HIPAA: Commodity Cloud Trap
AWS GovCloud and GCC High are not automatic compliance. See where commodity cloud breaks CMMC, HIPAA, FINRA, and attorney ethics, and when a private cloud wins.
Read post →
Data SovereigntyPrivate Cloud vs iCloud and Google Drive: Who Owns Data?
iCloud, Google Drive, and OneDrive are convenient, but your data lives on their terms. Why regulated and privacy-aware owners should evaluate a private cloud.
Read post →
Data ProtectionData Loss Prevention Strategy for 2026
Most sensitive data leaves through honest mistakes, not malice. Build a DLP program that covers email, endpoints, SaaS, and the audit evidence auditors expect.
Read post →
Network SecurityNetwork Segmentation Best Practices Guide
After initial access the attacker moves laterally. This segmentation guide covers VLAN design, microsegmentation, east-west controls, and the evidence auditors want.
Read post →
Pen TestingPenetration Testing Methodology Explained
Every organization has security gaps. Learn the reconnaissance, exploitation, post-exploit, and reporting stages ethical hackers follow, and what to buy.
Read post →
Zero TrustZero Trust Rules for GenAI Email Triage and HIPAA-Safe
Healthcare teams use GenAI to triage patient email. Here are the Zero Trust rules that keep the workflow HIPAA-safe and auditable.
Read post →
Zero TrustZero Trust with Passkeys for Customer Identity
Passkey-based customer identity in contact centers: how to combine Zero Trust, passkeys, and agent tooling for safer identity verification at scale.
Read post →
Zero TrustZero Trust for Agentic CRM Data Sharing Without Shadow Work
Grant AI agents minimum-scope CRM access, prove every action was sanctioned, and avoid the shadow work that auditors flag.
Read post →
CMMC ToolFree CMMC Self-Score Worksheet
Score your current CMMC readiness across the 110 NIST 800-171 controls in one downloadable worksheet. See where gaps live before a C3PAO visit.
Read post →
Local SEOAI SEO for Small Business: Get Found in 2026
How small businesses can use AI for SEO in 2026. Covers AI content tools, Google AI Overviews, local SEO automation, and getting cited by ChatGPT and Perplexity.
Read post →
Local SEOGoogle Maps SEO: Rank Your Business in 2026
Complete Google Business Profile optimization guide. Rank higher in Google Maps with NAP consistency, reviews, photos, posts, and local SEO strategies.
Read post →
 SMB Security
SMB Security10 Cybersecurity Tips for Small Businesses
The ten highest-leverage security moves a small business can make this quarter. Written for owners who have to make every dollar count.
Read guide →
Endpoint3 Ways Old Antivirus Leaves Your Business Vulnerable
Traditional antivirus missed modern ransomware, fileless malware, and living-off-the-land attacks. Here is what to replace it with, and why.
Read guide →
RansomwareWannaCry Ransomware: Field Notes and Lessons
The WannaCry outbreak reshaped how Petronella Technology Group runs ransomware defense. These field notes explain what still protects businesses today.
Read guide →
Private AI for CTOs: Why Regulated Teams Leave ChatGPT
Why mid-market CTOs in healthcare, defense, and finance are pulling AI workloads in-house, and what the production architecture looks like.
Read post → Private AIPrivate AI vs Cloud AI: Enterprise On-Premise Comparison
Side-by-side cost, latency, data-sovereignty, and compliance comparison for teams choosing between cloud APIs and on-prem inference.
Read post → AI SecurityAI Threat Detection 2026: How AI Transforms Cybersecurity
Where AI genuinely improves SOC outcomes, where it generates false confidence, and the human controls that keep automated response sane.
Read post → AI GovernanceAI Governance for Business: A Practical Framework Guide
A workable governance model: roles, review gates, model registries, and the policy artifacts auditors and the board both want.
Read post → AI InfrastructureAI Workstation vs Cloud GPU: 2026 Cost Guide
Real numbers from real builds: when an in-office workstation pays back faster than rented GPU minutes, and when it does not.
Read post → Private AIPrivate LLM Deployment: Run AI Without the Cloud in 2026
Reference architecture for self-hosted Llama, Mistral, and Qwen workloads behind your firewall, including hardware sizing.
Read post → AI for RetailAI for Retail: Demand Forecasting and Inventory Optimization
How retailers use private AI for demand forecasting, inventory optimization, and loss prevention without shipping sales data to a public model.
Read post → AI SecurityApril Fools Cyber Drill for GenAI Apps Without the Pranks
A tabletop red-team exercise for generative AI applications - run a controlled drill against prompt injection and data leakage without disrupting production.
Read post → AI SecurityCX That Outsmarts Deepfakes and Voice Clones
How customer-experience teams verify identity and harden voice channels against deepfake audio and AI voice cloning without adding friction for real callers.
Read post → AI GovernanceHard-Won Lessons from Rolling Out Microsoft Copilot at Scale
What enterprise Copilot deployments teach about data-access scoping, oversharing risk, and the governance controls regulated teams need before going wide.
Read post → AI SecurityDon't Get Pranked: Red Team Your AI Before They Do
A practical guide to red-teaming your AI systems - the prompt-injection, jailbreak, and data-exfiltration tests to run before an attacker finds the gaps first.
Read post → AI SecurityOutsmart Deepfakes in Your Contact Center
Deepfake voice attacks are targeting contact centers. The caller-verification, liveness, and agent-training controls that stop AI voice clones from social-engineering your staff.
Read post →
Incident Response Retainer: Why Every Business Needs One Before a Breach
What a retainer actually buys you, the response-time math, and how to evaluate IR firms before you have an emergency on your hands.
Read post → Incident ResponseIncident Response Plan Template: Free Download Guide
Six-phase IR plan template aligned with NIST SP 800-61, with role assignments, communications scripts, and notification triggers ready to fill in.
Read post → AwarenessPhishing Simulation Training: Build a Human Firewall
How to design a phishing simulation program that lowers click rates without burning out staff or generating compliance theater.
Read post → AwarenessRansomware Training for Employees: Prevention Program
What the training curriculum should cover, who should attend, how often to refresh, and the metrics that prove it actually changed behavior.
Read post → Zero TrustZero Trust Security Model: A Complete Business Guide
Zero trust without the buzzwords: identity, device posture, network segmentation, and the realistic 12 to 18-month rollout for mid-market.
Read post → Zero TrustTop 10 Zero Trust Vendors for SMBs 2026: Price and Features
Side-by-side scorecard of the ten zero-trust platforms that actually price and deploy for sub-thousand-seat organizations.
Read post → Zero TrustZero Trust vs VPN: Modern Remote Access in 2026
Why zero trust network access is replacing the legacy VPN, the security gaps a flat VPN tunnel leaves open, and a realistic migration path for mid-market teams.
Read post → AuditCyber Security Audit Checklist (2026): 60+ Items
The internal-audit checklist our vCISO team uses for quarterly client reviews, structured around CIS Controls v8 and NIST CSF 2.0.
Read post →
 AI Agents
AI AgentsOpenClaw: Open-Source AI Agent Framework Guide
Practical setup, configuration, and security review of the open-source agent framework our team uses for internal automation.
Read post →
AI DevAI-Powered Development with Claude Code: Workflow Guide
How an MSP and security team uses an AI coding assistant safely, including prompt scoping, secret hygiene, and review gates.
Read post →
AI AutomationAI Automation for Small Business: Save 20+ Hours a Week
Concrete automation patterns for back-office work that survive audit, with examples from finance, scheduling, and customer support.
Read post →
Custom AICustom AI Chatbot Development for Business
What goes into a defensible custom chatbot: data sourcing, retrieval design, guardrails, evaluation, and the part most vendors skip.
Read post →
 Claude
ClaudeClaude Design Principles for Regulated AI Builds
How Anthropic's Claude design and safety-first philosophy translates into production AI tooling for regulated industries. Lessons from Raleigh NC.
Read post →
ClaudeThe Claude Mythos: Why Anthropic Is Winning Enterprise AI
Why Claude overtook OpenAI in enterprise AI share, what Constitutional AI means for regulated industries, and how Petronella built its agent fleet on it.
Read post →
Claude SDKClaude SDK: Ship Production AI Agents Safely
Build production AI agents on the Claude SDK. Petronella Technology Group shows the architecture, tool use, prompt caching, rate limits, and test harness.
Read post →
ClaudePaperclip for Claude: How to Vet AI Extensions Safely
Paperclip for Claude turns Claude Code agents into a coordinated team. What it does, where the risks sit, and how to vet plugins before touching client data.
Read post →
AI ToolingCmux: The AI Agent Terminal for Regulated Dev Shops
What Cmux is, how it compares to tmux and Zellij, and the compliance questions Raleigh dev teams must answer before giving AI assistants shell access.
Read post →
AI CodingOpenCode, Antigravity, and Gemma 4: Safe AI Coding Tools
Comparing OpenCode, Google Antigravity, and Gemma 4 for CMMC and HIPAA-regulated teams. Which AI coding tools keep code local, and which ship it to the cloud?
Read post →
AI CodingPi.dev Review: Terminal Coding Agent for Regulated Teams
Pi.dev is a minimal open-source terminal coding agent. Review covers what it does, the install, the risks for regulated businesses, and how to adopt safely.
Read post →
Open Source AIHermes Agent: Open-Source AI for Regulated Businesses
Hermes Agent from Nous Research runs self-hosted AI on your own infrastructure. See when it beats Claude and GPT for CMMC, HIPAA, and data sovereignty.
Read post →
Local AIJan AI Review: Local-First LLMs for Regulated Businesses
Honest review of Jan AI, the open-source local-first ChatGPT alternative. When it fits regulated businesses and when you outgrow it for a private AI cluster.
Read post →
AI ResearchKarpathy's Autoresearch: What It Means for Enterprise R&D
Andrej Karpathy's autoresearch loop runs AI experiments overnight on a single GPU. Here is what it means for regulated businesses and how to experiment safely.
Read post →
AI VideoSeedance 2.0 for Business Video: What Owners Need to Know
Seedance 2.0 is ByteDance's new AI video model. How it compares to Sora 2, Veo 3, Runway, Kling, and Pika, with a compliance and brand-safety lens for owners.
Read post →
AI HardwareAI Workstation 2026: RTX 5090 Deep Learning Build
Full build guide for a 2026 AI workstation built around the RTX 5090, covering chassis, thermals, CUDA toolchain, and the deep-learning workloads it handles.
Read post →
InfrastructureMigrate VMware ESXi to Proxmox VE: Step by Step
Complete migration runbook for moving production workloads off VMware ESXi to Proxmox VE, with pre-flight checks, network mapping, and rollback paths.
Read post →
BackupProxmox Backup Server: Production Configuration Guide
Configure Proxmox Backup Server for real-world recovery: datastores, verification, garbage collection, encryption, and restore drills that actually work.
Read post →
InfrastructureProxmox vs Docker: When to Use Each in 2026
Virtualization or containers. Both earn their keep. This guide explains when Proxmox belongs in the stack, when Docker wins, and how they compose cleanly.
Read post →
HostingWordPress Migration Guide: Keep SEO, Move Off Slow Hosts
Step-by-step WordPress migration guide from Wix, Squarespace, Joomla, Drupal, or slow shared hosting. Preserve SEO, minimize downtime, and keep every ranking.
Read post →
HostingFrom GoDaddy to Custom Managed Hosting: Business Case
GoDaddy shared hosting throttles CPU, pushes upsells, and carries a documented FTC security record. Petronella offers faster, safer custom managed hosting.
Read post →
 CMMC
CMMCCMMC Enclave: Strategy, Tradeoffs, and 2026 Options
A 2026 guide to CMMC enclaves: segmentation, build versus buy, monthly cost ranges, failure modes, and evidence collection.
Read post →
CMMCCMMC Level 2 Checklist: 14 Domain Readiness Guide
A practical CMMC Level 2 checklist walking through all 14 NIST 800-171 domains, common gaps, and when to bring in a C3PAO.
Read post →
CompliancePrivate Cloud for CMMC and HIPAA: Commodity Cloud Trap
AWS GovCloud and GCC High are not automatic compliance. See where commodity cloud breaks CMMC, HIPAA, FINRA, and attorney ethics, and when a private cloud wins.
Read post →
Data SovereigntyPrivate Cloud vs iCloud and Google Drive: Who Owns Data?
iCloud, Google Drive, and OneDrive are convenient, but your data lives on their terms. Why regulated and privacy-aware owners should evaluate a private cloud.
Read post →
Data ProtectionData Loss Prevention Strategy for 2026
Most sensitive data leaves through honest mistakes, not malice. Build a DLP program that covers email, endpoints, SaaS, and the audit evidence auditors expect.
Read post →
Network SecurityNetwork Segmentation Best Practices Guide
After initial access the attacker moves laterally. This segmentation guide covers VLAN design, microsegmentation, east-west controls, and the evidence auditors want.
Read post →
Pen TestingPenetration Testing Methodology Explained
Every organization has security gaps. Learn the reconnaissance, exploitation, post-exploit, and reporting stages ethical hackers follow, and what to buy.
Read post →
Zero TrustZero Trust Rules for GenAI Email Triage and HIPAA-Safe
Healthcare teams use GenAI to triage patient email. Here are the Zero Trust rules that keep the workflow HIPAA-safe and auditable.
Read post →
Zero TrustZero Trust with Passkeys for Customer Identity
Passkey-based customer identity in contact centers: how to combine Zero Trust, passkeys, and agent tooling for safer identity verification at scale.
Read post →
Zero TrustZero Trust for Agentic CRM Data Sharing Without Shadow Work
Grant AI agents minimum-scope CRM access, prove every action was sanctioned, and avoid the shadow work that auditors flag.
Read post →
CMMC ToolFree CMMC Self-Score Worksheet
Score your current CMMC readiness across the 110 NIST 800-171 controls in one downloadable worksheet. See where gaps live before a C3PAO visit.
Read post →
Local SEOAI SEO for Small Business: Get Found in 2026
How small businesses can use AI for SEO in 2026. Covers AI content tools, Google AI Overviews, local SEO automation, and getting cited by ChatGPT and Perplexity.
Read post →
Local SEOGoogle Maps SEO: Rank Your Business in 2026
Complete Google Business Profile optimization guide. Rank higher in Google Maps with NAP consistency, reviews, photos, posts, and local SEO strategies.
Read post →
 SMB Security
SMB Security10 Cybersecurity Tips for Small Businesses
The ten highest-leverage security moves a small business can make this quarter. Written for owners who have to make every dollar count.
Read guide →
Endpoint3 Ways Old Antivirus Leaves Your Business Vulnerable
Traditional antivirus missed modern ransomware, fileless malware, and living-off-the-land attacks. Here is what to replace it with, and why.
Read guide →
RansomwareWannaCry Ransomware: Field Notes and Lessons
The WannaCry outbreak reshaped how Petronella Technology Group runs ransomware defense. These field notes explain what still protects businesses today.
Read guide →
OpenClaw: Open-Source AI Agent Framework Guide
Practical setup, configuration, and security review of the open-source agent framework our team uses for internal automation.
Read post → AI DevAI-Powered Development with Claude Code: Workflow Guide
How an MSP and security team uses an AI coding assistant safely, including prompt scoping, secret hygiene, and review gates.
Read post → AI AutomationAI Automation for Small Business: Save 20+ Hours a Week
Concrete automation patterns for back-office work that survive audit, with examples from finance, scheduling, and customer support.
Read post → Custom AICustom AI Chatbot Development for Business
What goes into a defensible custom chatbot: data sourcing, retrieval design, guardrails, evaluation, and the part most vendors skip.
Read post →
Claude Design Principles for Regulated AI Builds
How Anthropic's Claude design and safety-first philosophy translates into production AI tooling for regulated industries. Lessons from Raleigh NC.
Read post → ClaudeThe Claude Mythos: Why Anthropic Is Winning Enterprise AI
Why Claude overtook OpenAI in enterprise AI share, what Constitutional AI means for regulated industries, and how Petronella built its agent fleet on it.
Read post → Claude SDKClaude SDK: Ship Production AI Agents Safely
Build production AI agents on the Claude SDK. Petronella Technology Group shows the architecture, tool use, prompt caching, rate limits, and test harness.
Read post → ClaudePaperclip for Claude: How to Vet AI Extensions Safely
Paperclip for Claude turns Claude Code agents into a coordinated team. What it does, where the risks sit, and how to vet plugins before touching client data.
Read post → AI ToolingCmux: The AI Agent Terminal for Regulated Dev Shops
What Cmux is, how it compares to tmux and Zellij, and the compliance questions Raleigh dev teams must answer before giving AI assistants shell access.
Read post → AI CodingOpenCode, Antigravity, and Gemma 4: Safe AI Coding Tools
Comparing OpenCode, Google Antigravity, and Gemma 4 for CMMC and HIPAA-regulated teams. Which AI coding tools keep code local, and which ship it to the cloud?
Read post → AI CodingPi.dev Review: Terminal Coding Agent for Regulated Teams
Pi.dev is a minimal open-source terminal coding agent. Review covers what it does, the install, the risks for regulated businesses, and how to adopt safely.
Read post → Open Source AIHermes Agent: Open-Source AI for Regulated Businesses
Hermes Agent from Nous Research runs self-hosted AI on your own infrastructure. See when it beats Claude and GPT for CMMC, HIPAA, and data sovereignty.
Read post → Local AIJan AI Review: Local-First LLMs for Regulated Businesses
Honest review of Jan AI, the open-source local-first ChatGPT alternative. When it fits regulated businesses and when you outgrow it for a private AI cluster.
Read post → AI ResearchKarpathy's Autoresearch: What It Means for Enterprise R&D
Andrej Karpathy's autoresearch loop runs AI experiments overnight on a single GPU. Here is what it means for regulated businesses and how to experiment safely.
Read post → AI VideoSeedance 2.0 for Business Video: What Owners Need to Know
Seedance 2.0 is ByteDance's new AI video model. How it compares to Sora 2, Veo 3, Runway, Kling, and Pika, with a compliance and brand-safety lens for owners.
Read post → AI HardwareAI Workstation 2026: RTX 5090 Deep Learning Build
Full build guide for a 2026 AI workstation built around the RTX 5090, covering chassis, thermals, CUDA toolchain, and the deep-learning workloads it handles.
Read post → InfrastructureMigrate VMware ESXi to Proxmox VE: Step by Step
Complete migration runbook for moving production workloads off VMware ESXi to Proxmox VE, with pre-flight checks, network mapping, and rollback paths.
Read post → BackupProxmox Backup Server: Production Configuration Guide
Configure Proxmox Backup Server for real-world recovery: datastores, verification, garbage collection, encryption, and restore drills that actually work.
Read post → InfrastructureProxmox vs Docker: When to Use Each in 2026
Virtualization or containers. Both earn their keep. This guide explains when Proxmox belongs in the stack, when Docker wins, and how they compose cleanly.
Read post → HostingWordPress Migration Guide: Keep SEO, Move Off Slow Hosts
Step-by-step WordPress migration guide from Wix, Squarespace, Joomla, Drupal, or slow shared hosting. Preserve SEO, minimize downtime, and keep every ranking.
Read post → HostingFrom GoDaddy to Custom Managed Hosting: Business Case
GoDaddy shared hosting throttles CPU, pushes upsells, and carries a documented FTC security record. Petronella offers faster, safer custom managed hosting.
Read post →
 CMMC
CMMCCMMC Enclave: Strategy, Tradeoffs, and 2026 Options
A 2026 guide to CMMC enclaves: segmentation, build versus buy, monthly cost ranges, failure modes, and evidence collection.
Read post →
CMMCCMMC Level 2 Checklist: 14 Domain Readiness Guide
A practical CMMC Level 2 checklist walking through all 14 NIST 800-171 domains, common gaps, and when to bring in a C3PAO.
Read post →
CompliancePrivate Cloud for CMMC and HIPAA: Commodity Cloud Trap
AWS GovCloud and GCC High are not automatic compliance. See where commodity cloud breaks CMMC, HIPAA, FINRA, and attorney ethics, and when a private cloud wins.
Read post →
Data SovereigntyPrivate Cloud vs iCloud and Google Drive: Who Owns Data?
iCloud, Google Drive, and OneDrive are convenient, but your data lives on their terms. Why regulated and privacy-aware owners should evaluate a private cloud.
Read post →
Data ProtectionData Loss Prevention Strategy for 2026
Most sensitive data leaves through honest mistakes, not malice. Build a DLP program that covers email, endpoints, SaaS, and the audit evidence auditors expect.
Read post →
Network SecurityNetwork Segmentation Best Practices Guide
After initial access the attacker moves laterally. This segmentation guide covers VLAN design, microsegmentation, east-west controls, and the evidence auditors want.
Read post →
Pen TestingPenetration Testing Methodology Explained
Every organization has security gaps. Learn the reconnaissance, exploitation, post-exploit, and reporting stages ethical hackers follow, and what to buy.
Read post →
Zero TrustZero Trust Rules for GenAI Email Triage and HIPAA-Safe
Healthcare teams use GenAI to triage patient email. Here are the Zero Trust rules that keep the workflow HIPAA-safe and auditable.
Read post →
Zero TrustZero Trust with Passkeys for Customer Identity
Passkey-based customer identity in contact centers: how to combine Zero Trust, passkeys, and agent tooling for safer identity verification at scale.
Read post →
Zero TrustZero Trust for Agentic CRM Data Sharing Without Shadow Work
Grant AI agents minimum-scope CRM access, prove every action was sanctioned, and avoid the shadow work that auditors flag.
Read post →
CMMC ToolFree CMMC Self-Score Worksheet
Score your current CMMC readiness across the 110 NIST 800-171 controls in one downloadable worksheet. See where gaps live before a C3PAO visit.
Read post →
Local SEOAI SEO for Small Business: Get Found in 2026
How small businesses can use AI for SEO in 2026. Covers AI content tools, Google AI Overviews, local SEO automation, and getting cited by ChatGPT and Perplexity.
Read post →
Local SEOGoogle Maps SEO: Rank Your Business in 2026
Complete Google Business Profile optimization guide. Rank higher in Google Maps with NAP consistency, reviews, photos, posts, and local SEO strategies.
Read post →
 SMB Security
SMB Security10 Cybersecurity Tips for Small Businesses
The ten highest-leverage security moves a small business can make this quarter. Written for owners who have to make every dollar count.
Read guide →
Endpoint3 Ways Old Antivirus Leaves Your Business Vulnerable
Traditional antivirus missed modern ransomware, fileless malware, and living-off-the-land attacks. Here is what to replace it with, and why.
Read guide →
RansomwareWannaCry Ransomware: Field Notes and Lessons
The WannaCry outbreak reshaped how Petronella Technology Group runs ransomware defense. These field notes explain what still protects businesses today.
Read guide →
CMMC Enclave: Strategy, Tradeoffs, and 2026 Options
A 2026 guide to CMMC enclaves: segmentation, build versus buy, monthly cost ranges, failure modes, and evidence collection.
Read post → CMMCCMMC Level 2 Checklist: 14 Domain Readiness Guide
A practical CMMC Level 2 checklist walking through all 14 NIST 800-171 domains, common gaps, and when to bring in a C3PAO.
Read post → CompliancePrivate Cloud for CMMC and HIPAA: Commodity Cloud Trap
AWS GovCloud and GCC High are not automatic compliance. See where commodity cloud breaks CMMC, HIPAA, FINRA, and attorney ethics, and when a private cloud wins.
Read post → Data SovereigntyPrivate Cloud vs iCloud and Google Drive: Who Owns Data?
iCloud, Google Drive, and OneDrive are convenient, but your data lives on their terms. Why regulated and privacy-aware owners should evaluate a private cloud.
Read post → Data ProtectionData Loss Prevention Strategy for 2026
Most sensitive data leaves through honest mistakes, not malice. Build a DLP program that covers email, endpoints, SaaS, and the audit evidence auditors expect.
Read post → Network SecurityNetwork Segmentation Best Practices Guide
After initial access the attacker moves laterally. This segmentation guide covers VLAN design, microsegmentation, east-west controls, and the evidence auditors want.
Read post → Pen TestingPenetration Testing Methodology Explained
Every organization has security gaps. Learn the reconnaissance, exploitation, post-exploit, and reporting stages ethical hackers follow, and what to buy.
Read post → Zero TrustZero Trust Rules for GenAI Email Triage and HIPAA-Safe
Healthcare teams use GenAI to triage patient email. Here are the Zero Trust rules that keep the workflow HIPAA-safe and auditable.
Read post → Zero TrustZero Trust with Passkeys for Customer Identity
Passkey-based customer identity in contact centers: how to combine Zero Trust, passkeys, and agent tooling for safer identity verification at scale.
Read post → Zero TrustZero Trust for Agentic CRM Data Sharing Without Shadow Work
Grant AI agents minimum-scope CRM access, prove every action was sanctioned, and avoid the shadow work that auditors flag.
Read post → CMMC ToolFree CMMC Self-Score Worksheet
Score your current CMMC readiness across the 110 NIST 800-171 controls in one downloadable worksheet. See where gaps live before a C3PAO visit.
Read post → Local SEOAI SEO for Small Business: Get Found in 2026
How small businesses can use AI for SEO in 2026. Covers AI content tools, Google AI Overviews, local SEO automation, and getting cited by ChatGPT and Perplexity.
Read post → Local SEOGoogle Maps SEO: Rank Your Business in 2026
Complete Google Business Profile optimization guide. Rank higher in Google Maps with NAP consistency, reviews, photos, posts, and local SEO strategies.
Read post →
10 Cybersecurity Tips for Small Businesses
The ten highest-leverage security moves a small business can make this quarter. Written for owners who have to make every dollar count.
Read guide → Endpoint3 Ways Old Antivirus Leaves Your Business Vulnerable
Traditional antivirus missed modern ransomware, fileless malware, and living-off-the-land attacks. Here is what to replace it with, and why.
Read guide → RansomwareWannaCry Ransomware: Field Notes and Lessons
The WannaCry outbreak reshaped how Petronella Technology Group runs ransomware defense. These field notes explain what still protects businesses today.
Read guide →
On-Demand Training and Certification
For teams that want structured learning instead of scattered blog posts. The Petronella Training Academy is a subscription LMS with cohort-style and self-paced tracks across cybersecurity, AI, compliance, and the operating playbook our own MSP runs on.
The Academy works well for three audiences. First, internal IT and security teams that need consistent, role-aligned training instead of cobbling together vendor courses. Second, MSPs and IT services firms that subscribe to the Partner Program for white-label playbooks, sales templates, and the Operator Council. Third, business owners who want their staff trained on phishing resilience, AI safety, and HIPAA basics without the dry e-learning feel.
Tracks include CMMC fundamentals, HIPAA workforce training, private AI deployment, vCISO operations, and the MSP Partner Program for owner-operators of IT service firms. New cohorts launch quarterly. See the catalog and pricing inside the Academy.
Podcast Appearances and Video Library
Long-form conversations on cybersecurity, AI, CMMC, and what is actually happening in the regulated mid-market. Use these for background while you commute, or send them to a leadership team that needs context before a strategy call.
Craig Petronella has been a recurring guest on cybersecurity, MSP, and small-business technology shows since the early 2000s, and the YouTube library mirrors the same teaching style as the blog: practical, opinionated, and grounded in what works inside real client engagements. Episodes cover ransomware response, CMMC certification storylines, the AI privacy debate, and post-incident lessons learned. New short-form clips and full-length podcast guest spots are added regularly.
Free Tools and Self-Service Assessments
Use these to baseline your current posture in an afternoon. Nothing here requires a sales call or credit card. Each tool is built from the same intake questions our analysts ask during paid assessments, so the output is genuinely useful even if you never become a Petronella client.
Security Risk Self-Assessment
Free Phishing Security Test
4-Pillar Security Risk Assessment
Data Breach Cost Calculator
CMMC 2.0 Readiness Checklist
HIPAA Policy Templates
Incident Response Plan Template
Compliance Audit Checklist
2026 Cybersecurity Statistics
IT Budget Spreadsheet
Personal Privacy Toolkit
Compliance Risk Assessment Service
Managed Cybersecurity Services
Dark Web Monitoring Services
More Guides, Offers, and Press
Shorter reference pages, gated tools, and archival reads from the Petronella library. Use these to deepen a specific topic, sign up for assessments, or browse historical field notes from past engagements.
AI Readiness Assessment Offer
CMMC Gap Assessment Offer
System Security Plan Template
CJIS Compliance Reference
ITAR Compliance Reference
SEC Cybersecurity Rules
Industries Overview
IT Services Raleigh Overview
IT Support
UnHackable Newsletter Signup
10 Symptoms of Power Problems
Archival Field Notes and Press
Cybersecurity Blog Archive
Archival cybersecurity field notes and opinion pieces from the Petronella Technology Group blog library.
Read post → Cyber InsuranceStringent Cyber Insurance Rules
How tightening cyber insurance underwriting is reshaping controls and renewal conversations for mid-market organizations.
Read post → Mobile SecurityAndroid Spy Apps: What Owners Should Know
How commercial spy-app tooling ends up on corporate Android devices, and the mobile hygiene steps that close that attack path.
Read post → Breach PostmortemNeiman Marcus Data Breach Lessons
What the Neiman Marcus breach taught us about point-of-sale monitoring, vendor risk, and breach notification timelines.
Read post → PressPetronella Featured on WRAL Channel 5
Local press coverage of Petronella Technology Group on WRAL Channel 5, covering cybersecurity guidance for North Carolina businesses.
Read post →
Compliance Framework Reference Library
Deep reference pages on every framework Petronella Technology Group implements end-to-end. Use these as starting points for scoping conversations with your auditor, attorney, or board.
Compliance framework documentation is, frankly, hard to read. The official NIST and CMMC source documents are written for assessors, not for the IT teams who actually have to implement the controls. The reference pages below translate the source material into plain English, group related controls so you can see how they cluster operationally, and flag the controls that consistently cause the most heartburn during real assessments. Use them when scoping a project, drafting a System Security Plan, or briefing a board on what your compliance posture actually means.
If you are working across multiple frameworks (which is most regulated organizations: a defense contractor with healthcare clients, a financial firm processing card data, a research university with both FERPA and CMMC obligations), the CMMC-to-NIST mapping page is the single most useful reference on this site. It shows which controls satisfy multiple frameworks simultaneously, so you do not end up writing five different versions of the same access-control policy.
Regional vCISO and HIPAA Service Spotlights
Virtual CISO, compliance advisory, and HIPAA consulting delivered to growing North Carolina communities. Each page covers local regulatory context, travel coverage, and the typical engagement shape for that community.
Resources by Industry
Every regulated industry has a different threat model, compliance posture, and operational reality. These industry pages collect the guides, blog posts, and assessments most relevant to each sector our team supports.
An IT director at a sixty-bed clinic does not have the same problems as an IT director at a twenty-person law firm or a defense subcontractor manufacturing components for a tier-one prime. They use different software, face different auditors, and worry about different attack patterns. The industry pages below collect the most relevant guides, blog posts, and case-study material for each sector. They are starting points, not exhaustive directories. If you do not see your industry called out specifically, the underlying compliance and security work usually maps to one of the existing pages: most professional services firms find what they need on the law firm and financial services pages, and most public-sector or grant-funded organizations find what they need on the non-profit and education resources.
Healthcare and Covered Entities
HIPAA, HITRUST, EHR security, telehealth privacy, and the operational realities of clinics, practices, and digital health firms.

Law Firms and Legal Services
Client confidentiality, eDiscovery readiness, ABA Formal Opinion 477R, encrypted communications, and ethical wall enforcement.

Financial Services
SOC 2, PCI DSS, FFIEC, vendor risk management, and the controls examiners actually look for in mid-market financial firms.
Manufacturing and Supply Chain
OT and IT convergence, ITAR, CMMC for primes and subs, IoT hardening, and the operational technology security stack.
Non-Profits
Donor data protection, grant compliance, low-cost security stacks, and the volunteer-staffing realities that change the IT calculus.
Free Reports and Downloads
Field-tested briefs Petronella Technology Group published over the last decade. Plain English, no fluff, immediate use. Each one comes out of a real client conversation that happened often enough to warrant writing down.
16 Critical Questions Before Hiring an IT Company
Top 10 Most Expensive Computer Disasters
Reliable Disaster Recovery Plan Test
Protecting Critical Business Data
Choosing an Honest Computer Repair Provider
5 Simple Ways to Avoid Spam
12 Signs Your Business is Ready for a Server
IT Support Services Overview
Current Press and Media Coverage
How to Use This Resource Library
A few common questions from IT leaders, compliance officers, and business owners using these resources for the first time.
Where should I start if I am new to all of this?
Are the free assessments and templates actually useful, or are they marketing fluff?
How do the blog and the flagship guides differ?
Can my team use these resources for our own internal training?
How often is this library updated?
Do you serve clients outside the Raleigh-Durham area?
I am an MSP or IT services firm. Is anything here useful to me?
What You Actually Get Inside Each Flagship Guide
Every one of our pillar guides is built from client work, not from desk research. Here is exactly what is inside each one, who it is written for, and the decisions it will help you make faster.
The CMMC Compliance Guide is a Registered Practitioner Organization's field manual for the Defense Industrial Base. It opens with a clear explanation of the CMMC 2.0 three-level structure, what changed from CMMC 1.0, and which level you are likely scoped for based on your contract CUI handling. Then it walks through the 110 NIST 800-171 controls grouped into the fourteen families, with notes on which ones consistently cause assessment findings. You will find a CUI scoping worksheet, a System Security Plan outline aligned to the 110 controls, a Plan of Action and Milestones template for documenting remediation, and a vendor-selection section covering C3PAO assessor choice and the supporting tooling. The guide is written for CEOs, CIOs, and IT directors at primes and subs between twenty and five hundred employees. If you are trying to decide whether to self-attest at Level 1, pursue Level 2 certification, or retire from defense work entirely, this guide will help you make that call with eyes open.
The HIPAA Compliance Guide is the practical companion to the Security Rule, Privacy Rule, and Breach Notification Rule. It covers the required and addressable implementation specifications, walks through the full security risk assessment workflow that satisfies the Office for Civil Rights, and lays out the 2026 Security Rule update timeline that many covered entities are still catching up on. Inside the guide you will find annual workforce training standards, encryption and access-control requirements for electronic protected health information, the Business Associate Agreement review checklist, and the incident response decision tree for breach notification. The guide is written for compliance officers, practice administrators, and IT leaders at clinics, practices, hospitals, digital health startups, and business associates. If you have ever had an OCR letter land on your desk and felt unsure whether your documentation would hold up under review, this guide is the thing you want sitting next to your risk register.
The AI Implementation Guide is our most requested download from CTOs and technology directors at regulated mid-market organizations. It answers the one question every technology leader is now being asked by a board or executive team: how do we use AI responsibly, given the data we handle. The guide covers private LLM hosting for sensitive workloads, the build-versus-buy-versus-fine-tune decision framework, hardware sizing for on-premise inference, retrieval-augmented generation for internal document access, model selection across the open-source ecosystem, guardrail design for HIPAA and CFR-controlled data, and the AI governance policies that satisfy both auditors and the board. It is written for CTOs, VPs of Engineering, CIOs, and senior technology leaders at healthcare, defense, finance, legal, and research organizations that cannot send production data to consumer AI products. If your team is under pressure to deploy AI but nobody is sure what the guardrails should look like, start here.
The Forensics Incident Response Playbook is the tactical guide for the worst week of your career. It is built from real ransomware recoveries, business email compromise investigations, SIM swap reversals, and cryptocurrency theft cases our team has worked through. The playbook covers the first-hour evidence preservation steps that preserve your legal options, the chain-of-custody documentation your cyber insurance carrier and attorneys will require, the communications sequencing for employees and customers and regulators, the network forensics workflow for identifying initial access and lateral movement, and the tabletop exercises your leadership team should run before a real incident. It is written for anyone who could conceivably be the first person at your organization to realize something is very wrong. That usually means the IT director, the security officer, the CFO, or the CEO. Reading the playbook before you need it turns the first four hours of an incident from panic into execution.
The MSP Accelerator Playbook is a different animal. Where the other guides are built for clients, this one is built for peer firms. It is the full operating playbook our team uses to run a profitable managed services and managed security practice: the service stack, the pricing tiers, the quarterly business review cadence, the documentation standards that let a new technician ramp in two weeks instead of two months, the referral network structure, and the Operator Council peer-group process that keeps our owner accountable to outside benchmarks. It is for managed services firm owners and leadership teams that want to grow margins without burning out the bench. Reading it will not replace the work, but it will save you a year of trial and error.
How Petronella Technology Group Builds Its Resource Library
The goal is not volume. The goal is that every resource on this page reflects work we have actually delivered for a client, a framework we have actually implemented, or an incident we have actually worked through.
Petronella Technology Group was founded in 2002 in Raleigh, NC, and has been operating in the Research Triangle continuously since. Across the team we hold CMMC Registered Practitioner credentials, a CCNA for network engineering, a CWNE for enterprise wireless, and the DFE #604180 digital forensics credential for our founder Craig Petronella. As an organization we are a CMMC-AB Registered Provider Organization (RPO #1449), listed publicly on the Cyber AB member directory, and a Better Business Bureau A+ rated firm continuously since 2003. Those credentials matter because they shape every resource on this page. The CMMC content comes from sitting across the table from real primes and real subs as they prepare for real assessments. The HIPAA content comes from delivering real security risk assessments and then defending the documentation when the Office for Civil Rights asked follow-up questions. The forensics content comes from actual ransomware recoveries, actual wire-fraud reversals, and actual network investigations we have executed on behalf of clients.
Editorially, we try to follow three rules. First, no speculative content. If we have not actually deployed it, advised on it, or recovered from it, we do not write about it as if we have. Second, no vendor-driven conclusions. Our blog post comparing CMMC documentation platforms, our post comparing zero-trust vendors, and our post comparing password managers were all written after actually running the tools side-by-side inside our own environment or for a client project. We are not paid by any of the vendors we cover, and we change our recommendations when the underlying products change. Third, no fabricated statistics. You will not find a cybersecurity-industry "ninety-five percent of breaches are caused by human error" line on this page unless we can point you to the primary source. When we cite a number, we cite where it came from and when it was measured.
Craig's professional background drives the forensics specialty specifically. Inside the broader forensics field we are focused on SIM swap reversal, cryptocurrency theft investigation, pig-butchering scam analysis, ransomware recovery, business email compromise, and network forensics for intrusion investigation. We are not a private investigation firm, we do not run a Cellebrite or Encase mobile-device lab, and we do not handle traditional e-discovery workstreams. When an incident requires those specialties, we coordinate with a trusted partner network while retaining the strategic and forensic role our credentials cover. That scoping shows up in the resource library: the forensics content you will find here is deep on what we do, and honest about what we do not.
Finally, the resource library is updated on a rolling basis, not on a marketing calendar. The blog publishes weekly on whatever topic is most active across our client base that week. Flagship guides are updated whenever the underlying regulation, framework, or technology changes materially. Free tools and assessment templates are refreshed whenever we update the internal version our analysts use on real engagements. If you find content that feels out of date, email craig at petronellatech.com with the URL and we will prioritize the update.
More Common Questions
Follow-up questions we hear from IT leaders, compliance officers, and owner-operators after they have spent time inside the resource library.
What is the difference between a CMMC gap assessment and a CMMC readiness review?
How do your guides stay current when frameworks and regulations keep changing?
Can I use these resources for internal employee training programs?
Do you offer any kind of free initial consultation?
What makes your CMMC work different from the big national consultancies?
I keep seeing "private AI" versus "cloud AI" debates. Which does Petronella Technology Group actually recommend?
How do I know if the free self-assessments are giving me accurate results?
Are all of these resources genuinely free, or is there a catch?
Want a Working Session With a Petronella Analyst?
If you have been through the resources here and want a real conversation about your environment, your compliance pressures, or your AI roadmap, schedule a free consultation. No sales script. Just a working call with a senior practitioner.
See also: FTC compliance training program.
See also: security awareness training program.
Featured Insights for Defense Contractors and IT Leaders
Recent guidance from Petronella Technology Group on CMMC, AI workflows, threat response, and regional service delivery in the Raleigh - Charlotte corridor.
CMMC + Compliance
- 3 New Compliance Courses 2026 Sat Cpa Ftc
- Cmmc Level 1 30 Day Self Assessment Playbook For Small nc Manufacturers
- Cmmc vs Nist 800 171 Complete Comparison 2026
- Complianceforge Alternative Cmmc Rpo 2026
- Cui Handler Field Manual 2026
- Cui vs Fci Defense Contractor Guide
- Dfars Clauses Cmmc Field Guide 2026
- How to Calculate Your Sprs Score
AI + Automation
- ai Acceptable Use Policy Stop Pretending Your Team Isn t Using Chatgpt
- ai Coding Workflow 22 Moves to Ship Safely
- ai Driven Redaction That Keeps Customer Data Audit Safe
- ai Escalation Playbooks to Stop Repeat Contacts
- ai Readiness Checklist What Your Score is Really Telling You
- ai Triage For Contact Center qa to Protect Customer Trust
- ai Vocabulary For Vibe Coders 5 Terms Before You Ship
- Audit Proof Incident Response Runbooks For ai Systems
- Git For Vibe Coders Survival Guide
- How to Build Private Llm Business Without Phd
- Keeping Coding Agents Safe With ai Supply Chain Guards
- Zero Disclosure ai Private Search For Regulated Data
- Zero Trust Data Sharing For Partner ai Training
- Zero Trust For Contact Centers Ensuring ai Access
Regional Services
- Best Managed it Service Providers Raleigh nc 2026
- Cybersecurity Raleigh nc
- Cybersecurity Services Charlotte nc Protect Your Business
- Managed it Services Charlotte Smb 2026 Comparison
- Managed it Services Raleigh 2026 Smb Buyer s Guide
- Managed Service Provider Raleigh
Infrastructure + Resilience
- Blockchain Proof For Sustainable Supply Chains no Claims
- Dgx Spark Cluster Cables in Stock 0 5m Qsfp112 400g Dac For Every Gb10 Workstation 159 ...
- Iot Pump Analytics Predict Downtime And Audit Logs
- is Proxmox Free Enterprise Licensing Explained 2026
Featured Articles
Incident + Threat
- How to Recover From Ransomware
- Memorial Day Cyber Incident Drills For Business Resilience
- Phishing Resistant Mfa a 5 Step Rollout Plan For 25 Endpoint Smb Clients in Regulated I...
- Ransomware Checklist Your First Hour Decides The Bill
- What to do After a Data Breach
- Zero Trust Vendor Selection Checklist For Smbs 2026